ChatGPT makes the GPT-3 large language model usable in conversational scenarios. What impact will this have?

Facial recognition is becoming more and more common. In some cases, it’s used to make existing procedures more efficient or to connect existing data points together. While that seems like the community has already consented to these use cases, people often have a visceral reaction to hearing that new technology is being applied.

Apple is under fire on a number of fronts. The biggest issue this week is several bills introduced in the US. A key issue? The ability to “sideload” apps on your iPhone.

Apples annual developer conference announced the latest version of all of Apples operating sytems and privacy was a key pillar across all of them.

Trying to come up to speed on cloud security at AWS re:Invent 2022? Here’s my session guide for attendees of all levels.

CJ Moses, CISO of AWS, delivers a leadership session to highlight the state of security and what’s next.
Highlights from Dr. Werner Vogel’s keynote at AWS re:Invent 2022.

Trying to come up to speed on cloud security at AWS re:Invent 2022? Here’s my session guide for attendees of all levels.

CJ Moses, CISO of AWS, delivers a leadership session to highlight the state of security and what’s next.
Highlights from Dr. Werner Vogel’s keynote at AWS re:Invent 2022.

Microsoft Build 2014 kicks off a new era for Microsoft. One that will (hopefully) transform the company and focus on building out their cloud; Azure.
ChatGPT makes the GPT-3 large language model usable in conversational scenarios. What impact will this have?

Mastodon is an open-source federated social media network. Twitter users are flocking to it only to find furstration.

The EU has mandated all smartphones use USB-C to charge by 2024, all laptops by 2026. It’s about time.

Trying to come up to speed on cloud security at AWS re:Invent 2022? Here’s my session guide for attendees of all levels.

CJ Moses, CISO of AWS, delivers a leadership session to highlight the state of security and what’s next.
Highlights from Dr. Werner Vogel’s keynote at AWS re:Invent 2022.
Parler gets deplatformed and can’t find any organizations that want to work with it. It’s about time.

Outages are hard to handle. There’s pressure to get things back up and running, to avoid damage to your reputation, and to avoid getting yelled at by the boss. The Help Desk is often the best positioned team to help…and the most overlooked. Here are some tips to help handle the communications side of incidents better.

Is working from home the new normal in tech? Is working from home as simple as ensuring a strong internet connection and access to the right tools? This is an issue with a ton of impacts outside of just the relationships on your team. This post highlights various conversations and points of view on the issue.

Twitch has been hit by a major data breach. 165GB of critical information was leaked on 4chan. What will the impact be? Will this cause even more streamers to leave?

A new report from a United States Senate Committee gave 24 US department and agencies an average grade of C- in cybersecurity. That’s not good.

The region of Lazio was hit by a ransomware attack and is struggling to recover from this attack on critical infrastructure. BlackMatter, a new ransomware supergroup, just announced they wouldn’t conduct these types of attacks. What does it mean for the future of ransomware?

The included_files feature of Netlify Functions can be confusing. Here’s how to get it working.

I’ve been publishing to markn.ca for almost 22 years. I broke it yet again in order to fix it.

In software, developers often don’t have a choice. Speed becomes a business imperative for survival and to stay competitive.

Google Cloud makes some small pricing adjustments and reactions are mixed. Here are my thoughts.

Google Cloud recently cleaned up both the CLIs and SDKs for building in the Google Cloud.

Google Chrome OS Flex is going to help put Chrome OS on a lot more computers. That’s a good thing, right?

Canadian data privacy laws state that an organization is responsible for the life cycle of the data. Most orgs struggle with protecting it while it’s in use, what about after they no longer need it?
The Digital Economy Act of 2017 in the UK is trying to put up enforceable age gates to pornography. That might be a good idea but it’s extremely difficult to actual do online. At the same time, here in Canada, our major financial players are launching a joint identity service.
Connect both of these issues together and the larger issue …
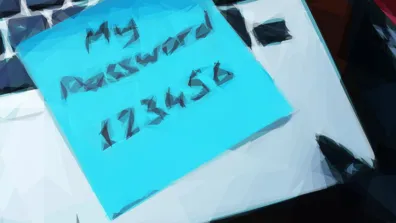
Security awareness is next to useless. Educate users instead
Some WD My Book Live users had a shock this week as hackers remotely wiped their data. What can they do about it?

When your local electric utility offered a new smart thermostat a heavy discount, a lot of homeowners jumped at the chance. Unfortunately, a clause in the terms of the promotion grants the utility access to your data and the ability to remotely control the device!

Colonial Pipeline is recovering from a ransomware cyberattack. There’s a ton of attention on them right now, what do you need to know about this issue?

Your centralized security needs to support a variety of teams building in the cloud…and they all have differing levels of maturity.

For stronger security, stop focusing on cybercriminals and pay attention to how your teams are building in the cloud.

AWS re:Inforce brought the people side of security into sharp focus.

Presenting on video and live streams is hard. Even though the goal is to connect to people, sitting alone(ish) presenting to a camera lens and computer display can be alienating. There are a number of simple techniques you can use to upgrade the quality of your present and stream. This post walks you through planning out and delivering a high …

Video conferencing platform Zoom has been in the news almost constantly over the past few weeks. At first it was hailed as a tool to help reduce this isolated feeling all of us are experiencing, then it was a pile on for security and privacy issues, and finally the last two weeks have started a redemption story.

AWS has recently explored with great machine learning services. From the core building blocks to services design to teach you techniques to simple transactional services that just get the job done. This stream looks provides an overview of these services and when you might want to use them.

Colonial Pipeline is recovering from a ransomware cyberattack. There’s a ton of attention on them right now, what do you need to know about this issue?

Nothing is built in isolation. Each technology builds on layers and layers of technology before it. But are those layers worth building on? Can they support the weight of new ideas? How do you account for issues in layers you don’ t control? We’re seeing the negative consequences more and more in the IIoT / OT world…
This deep techincal dive in the cybersecurity of operational technologies (OT) focuses on the dramatic timing disconnect. Physical technology is often bought to last for years and years, digitally focused tech is designed to be updated constantly and replaced quickly. That’s problem in today’s hostile internet.

Data Privacy Day is upon us once again, here’s an interesting discussion around key privacy topics and how they might impact you.

“Um” is not a great call to action, but sometimes it’s all you’ve got.

Toasters work so well that you forget they need maintenance. If we could get to taht level with cybersecurity controls we’d be lucky…until we weren’t
Are NFTs, Web3, and Blockchains useful? Or just hype?

The Twitter blue checkmark started as a security control and slowly turned into social status. What happened to the security part?

Trying to come up to speed on cloud security at AWS re:Invent 2022? Here’s my session guide for attendees of all levels.

CJ Moses, CISO of AWS, delivers a leadership session to highlight the state of security and what’s next.

The included_files feature of Netlify Functions can be confusing. Here’s how to get it working.

Serverless used to mean something…maybe. Does it mean anything to the cloud community today?

Serverless architectures help you and your team focus almost entirely on delivering business value. They also break almost every existing security technique. I’ve been actively researching serverless security for a while now, here’s what I’ve learned over the past three years.
Are NFTs, Web3, and Blockchains useful? Or just hype?

Two minutes of work can stop hackers in cold in their tracks.

The Twitter blue checkmark started as a security control and slowly turned into social status. What happened to the security part?

Mastodon is an open-source federated social media network. Twitter users are flocking to it only to find furstration.

If you’ve been harassed online, is there any hope that the criminal will be caught?

Facebook commits $10B per year to build the multiverse. Earnest attempt at progress or an attempt to divert attention?
Parler gets deplatformed and can’t find any organizations that want to work with it. It’s about time.

Is your day chalk full of video calls? Wondering why you’re exhausted at the end of the day? The two might be related 😉. In this column, Robyn and I discuss some of the reasons for ‘zoom fatigue’ and what technology might help address it.

The Unicorn Project is the latest book from Gene Kim, one of the leaders of the DevOps movement. The book focuses on developer enablement and culture. What does this have to do with cloud security? Everything.
The cloud is an amplifier. It lets teams do more with less. This innovative and fast-paced approach creates a mountain of security …
Security is often spoken of in absolutes. Is this secure? Is that insecure? The reality is that security is a spectrum. It is a series of implicit and explicit decisions made to meet the business needs within an acceptable risk tolerance.
What is an acceptable risk? How can you determine what threats pose a risk to your work? How likely are those …

Organizations struggle with extending their security practices to the cloud. Traditional approaches don’t work, and new cloud-only practices duplicate work for an already overtaxed team. The goal of cybersecurity is simple: to ensure that what you build works as intended and only as intended. This session teaches you how the AWS Cloud Adoption …
ChatGPT makes the GPT-3 large language model usable in conversational scenarios. What impact will this have?

The EU has mandated all smartphones use USB-C to charge by 2024, all laptops by 2026. It’s about time.

I’ve been publishing to markn.ca for almost 22 years. I broke it yet again in order to fix it.

The second series of my live streaming series for Trend Micro. In it,I speak to various cloud leaders about what’s happening in cloud.

In this live streaming series for Trend Micro, I speak to various cloud leaders about what’s happening in cloud.

Four principles to help you navigate a cloud migration and the realities of hybrid cloud.

The Pegasus Project is a collaborative effort by a number of media and advocacy organizations around to the world. With their work, they are shining a light on nation state use a specific malware tool: Pegasus spyware.
The out-of-band patch for PrinterNightmare on Microsoft Windows doesn’t completely fix the issue. What are IT and security teams to do?

PrinterNightmare is a high severity vulnerability that affects all versions of Windows and is being actively exploited…on a long weekend 😬