
Twitch has been hit by a major data breach. 165GB of critical information was leaked on 4chan. What will the impact be? Will this cause even more streamers to leave?

A new report from a United States Senate Committee gave 24 US department and agencies an average grade of C- in cybersecurity. That’s not good.

The region of Lazio was hit by a ransomware attack and is struggling to recover from this attack on critical infrastructure. BlackMatter, a new ransomware supergroup, just announced they wouldn’t conduct these types of attacks. What does it mean for the future of ransomware?

EA got hacked and 780 GB of source code was stolen. The hackers attempted to extort EA and when they didn’t pay, the data was dumped online.

Two new resources launched to help people understand the challenges associated with ransomware; StopRansomware.gov and RansomWhe.re

REvil has been one of the top ransomware groups for the past few months but they’re suddenly offline. No note, no warning, just gone.

Long after the headlines pass, victims of ransomware are left struggling to get back to “normal” operations. It’s a long, challenging road back.
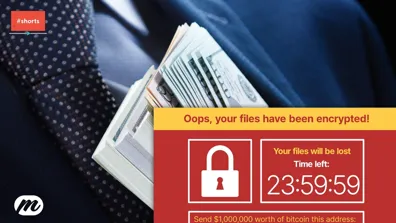
The REvil gang attack Kaseya, an IT management platform, and that got them access to 800—1,500 more businesses without any additional effort setting the new normal.

Ransomware is absolutely everywhere. What is going on? Why is ransomware so effective? Is there anything we can do about it?

Colonial Pipeline is recovering from a ransomware cyberattack. There’s a ton of attention on them right now, what do you need to know about this issue?

Emotet and NetWalker are both taken offline within days of each. A big wins for users, law enforcement, and international cooperation…at least for a little while.

The Canada Revenue Agency suffered a large breach exposing over 5,000 citizens to COVID-19 benefit fraud. This issue exposes some of the challenges of providing authentication services to millions of citizens. Why did this happen? And what can we do to protect ourselves?

Black Friday and Cybermonday are two of the biggest shopping days of the year. Consumers rush to get the biggest deals on all sorts of items. Sadly, scammers and cybercriminals also rush to take advantage.

Cybercriminals don’t always use complicated technical attacks to get around your cybersecurity. Sometimes—probably more often than we care to admit—it’s the really simple stuff that works and what’s simpler than an email?

We rely on some digital services for critical functions around security and privacy. Trusting those services is paramount to their success and ours. But it can be difficult to trust when you don’t know what’s going on behind the scenes. Gag orders from the courts can amplify those trust issues. The idea of a warrant canary can help to …
There has been a significant increase in DNS hijacking attacks over the past couple of months…and why not? It’s a simple, direct way for cybercriminals to take over an organizations identity or to intercept critical communications.

Cryptocurrencies have dropped in popularity and value but cybercriminals continue undeterred. The latest on cybercrime and cryptocurrency…

It’s not uncommon for cybercriminals to combine multiple data sets in order to increase their chances of finding valid user credentials. Security researcher Troy Hunt found the mother of all collections, dubbed “Collection #1”. This roll up contains 773M sets of credentials from various breaches.
But why does this work for …

How much can one jurisdiction affect the internet? Turns out, a lot. Recent actions by the US and Australia are having and could have a disproportionate impact on our online communities.

Cyberattack attribution is HARD. But time and time again, we’re seeing attributions—who carried out the attack—made publicly with little to no evidence presented. Worse, these attributions are having real world impacts…

Bloomberg has an absolutely earth shattering report citing a hardware supply chain attack that—they say—impacted several big names. Here’s why this type of attack is so difficult to defend against but also near impossible to execute.

Hackers and cybercriminals are all “malicious actors”. While you may not know who is attacking a system, having a better understanding of common motivations is important.

Cryptocurrency is a digital asset. As such, it’s a major target for cybercriminals. We’ve seen attack after attack in the past few months as exchanges, apps, and other players in the cryptocurrency market aren’t aligning their security to the threats they face.

Where does the Canadian criminal code stand on hacking? Given how fast technology moves, can the law keep up?
Is IP blocking still effective? Is it a sledge hammer when you really need a scalpel?

Accurate data for cybersecurity threats is hard to come by. That doesn’t mean you can just make it up…

CPU Vulnerabilities Seem Like A Massive Problem. Are they deserving of the hype?

DDoS attacks are scaling to new heights using record numbers of compromised machines. What are your responsibilities to the rest of internet community?

Cyberattacks happen all of the time. The critical angle to evaluate is their impact. Did the attack breach critical systems? Access personal information?

This post provides information that is designed to help you defend against phishing, spear phishing, and whaling attacks. Exploring the reasons for phishing, spear phishing, and whaling success