I spoke with Hallie Cotnam on CBC Ottawa Morning on 26-Aug-2022 about this issue.
The promise of the internet is that it can connect us all. It’s also a threat.
There are wonderful use cases of technology. Especially over the past few years with various lockdowns and travel restrictions. Being able to work remotely, connected with friends and family, and to stay entertained and informed has been invaluable.
The negative stories range from frustration to outright horror. Recently, Canadian journalist Raisa Patel had an experience that borders on outright horror.
Online Harassment
Raisa shares the start of her story in this Twitter thread.
🧵Long thread, but a summary of the past day: Yesterday, @angelynsayshi, @_jennamoon & I were targeted in the latest violent, misogynistic, racist campaign against Canadian journalists. We have decided to post it without censoring anything. TW for violence, racism, sexual assault pic.twitter.com/Do8ndP526v— Raisa Patel (@R_SPatel) August 11, 2022
Making matters worse is that when Raisa turned to the police for help, bureaucracy and poor experiences kicked in…
My police reporting update is that I spent a total of four hours on hold with the Ottawa Police Service today across two different attempts. On one call I was not able to speak to anyone after 1.5 hours on the line. Same result after spending 2.5 hours waiting on another attempt.— Raisa Patel (@R_SPatel) August 12, 2022
This experience is what prompted my conversation with Hallie. Is this common? Why are these hurdles in place? Is there actually any point in reporting these types of crime to police?
Why I’m qualified to write about this issue? I did my graduate work in digital forensics and worked as an investigator for several years. I continue to research and apply digital forensics techniques in my work. While my focus isn’t online harassment, the technological aspects are the same.
The social impacts are quite different which is why I refer to other experts in that space down below.
Technical Breadcrumbs
To identify and then track down a suspect in a case like this, a technical trail must be followed.
Using Ms. Patel’s case as an example, we start with an email. From the screenshots posted, that email came from an email account with the provider Proton.
Email providers will have differing amounts of information on their account holders. Proton is a privacy-focused provider offering free and paid accounts. By design, they store a minimal amount of information about their users.
For a free account, only a username and password is required. Paid accounts require some level of billing information. There’s a near endless list of email providers out there. When a suspect is looking to abuse the system, Proton’s design doesn’t actually impact the case much. Other providers might have more information, but the odds are good that it’s false.
Why would a suspect put in their actual name when “Sam Samington” or another made up name would work just as well?
The victim already has the actual email, so what we’re looking for from the provider is an IP address or other information that might lead to the person behind the malicious account.
Assuming that information is available. The IP address leads us to the next step in the trail.
Misdirection Connection
If you’ve been on YouTube in the last year, you’ve probably seen an ad for virtual private network or VPN . While positioned as privacy-protecting and an easy way to get access to geo-locked content, what a VPN really does it route all of your internet requests through the providers servers.
It’s a misdirect.
In a cybercrime situation, that means the IP address linked to the account at the email provider probably belongs to a VPN provider. That’s another round of requests and hopefully some account information for our investigation. It’ll depend on the provider and information associated with the account if anything useful comes from this step.
Odds a good—in a bad way—that there’s only another IP address at this step…that might lead to an internet service provider or ISP.
At this (hopefully) final step, the investigation might actually lead to an account information with accurate information linking all of this activity to an actual individual.
Who, Me?
…maybe.
An ISP or mobile provider account is actually just a link to who paid for the connection to the internet. The trail we’ve compiled so far has linked from a the offending email to a VPN to an ISP to an account.
This may or may not link to a specific device. For a mobile account, the technical information can more easily be linked to a specific device. It’s done that way for a billing purposes.
For a home or residential internet connection, that will link to a router.
This is the device that connects to everything in the residence to the internet. If there are several or several dozen devices in the house, which one sent the email?
This is when the technical investigation needs to move to the forensic examination of the all of the potential devices. The hope here is evidence that is sufficient to link a person to the action.
Until that happens, you don’t know which person actually sent the email. If could be anyone with access to that connection…which could include more than just the people authorized to access that connection.
That lack of certainty makes charging someone and being successful in their prosecution very difficult.
Paperwork, Paperwork, and More Paperwork
We’ve followed a typical technical trail for cases like this.
It’s complicated, involves multiple systems, lots of opportunity for data to be lost, and requires a lot of technical expertise to properly follow this trail. An even higher level of expertise is required to follow the trail with enough rigour and process to testify with credibility in court.
And that’s where the other set of challenge lie; the law.
The internet connects our planet. That’s often just accepted but really comes to light in situations like this. Imagine for a second that each of these steps lands the investigation in a different country.
For Raisa, this is what’s happening.
The email was sent through the Proton service. This service is run by a company in Switzerland and they follow Swiss law. That includes extremely strong privacy protections for individuals and depending on the situation, the European General Data Protection Regulation (GDPR) could also apply .
Here’s a great call out of the Swiss data protections by data hosting provider Artmotion. That’s easier to dig through than the actual legal statutes.
In order to get whatever information Proton has about the suspect, Canadian law enforcement must make a request in Switzerland under Swiss land. IANAL, but the long and short of it is that this is another layer of paperwork and another set of standards to apply.
Generally, at each step in the technical trail the following questions must be answered;
- Is what happened a crime in the country in question?
- Have the required standards been met for law enforcement/court ordered action to be taken?
- Are these sufficient resources in the country in question to address the issue?
- Can/will law enforcement in the originating question work through the process?
In our scenario so far, there’s at least two (Canada and Switzerland) and most likely four jurisdictions involved. How did we get to five?
- The victim is in Canada
- The original email was sent from Switzerland
- A VPN provider in another country
- The ISP/mobile provider in yet another country
- The suspect most likely is in the same jurisdiction as the ISP/mobile provider
Numbers 3—5 are assumptions, but given the pattern in the cases I’ve seen over the years they are most likely true.
That’s a lot.
Lack of Resources
The technical issues and bureaucracy are not insurmountable. They require patient and commitment to navigate, but it can be done.
A bigger, over-arching issue is the lack of available resources. This is technical law enforcement work. That’s a skillset in high demand both from a recruiting and deployment perspective.
Every country has this challenge. Here are a sample set of reporting from Canada, the USA, and Ireland. Many more are just an online search away. No one has enough resources to address crimes like this.
There is a finite set of resources that can be deployed to help solve crimes with an online component. We need to have a discussion in our communities as to what those resources should be prioritized for.
Right now, we’re not.
Occasionally we talk about harassment and cyberbullying. Child endangerment comes up often, but often as a club to push through laws that weaken encryption and reduce everyone’s digital security. Not to actually address long term protections.
Cybercrimes with financial impacts are in the news frequently, but only a few times a year do we see any successful legal actions being taken. It’s not from a lack of desire or bad intentions. It’s a systematic issue that’s only being addressed in a fragments.
Are victims like Raisa Patel, Angelyn Francis, Jenna Moon, and countless others left by the way side?
Steps To Protect Yourself
No. There are steps you can take to help reduce your online risk and the potential impacts from issues like this.
These steps are better laid out by experts in this space like Leigh Honeywell. Leigh is the CEO of Tall Poppy. Tall Poppy offers a set of tools from an amazing team that help “stop online harassment from escalating to hacking.” Organizations can—and should—add this to their benefits package to help their staff be safe and secure online.
No, I don’t work for Tall Poppy but I’m a huge fan of their work. This is a critical issue and they’re making it easier for people to get help while building a sustainable business. That’s to be admired
If you are responding to harassment like this and in immediate crisis, I’ll refer to Tall Poppy’s advice;
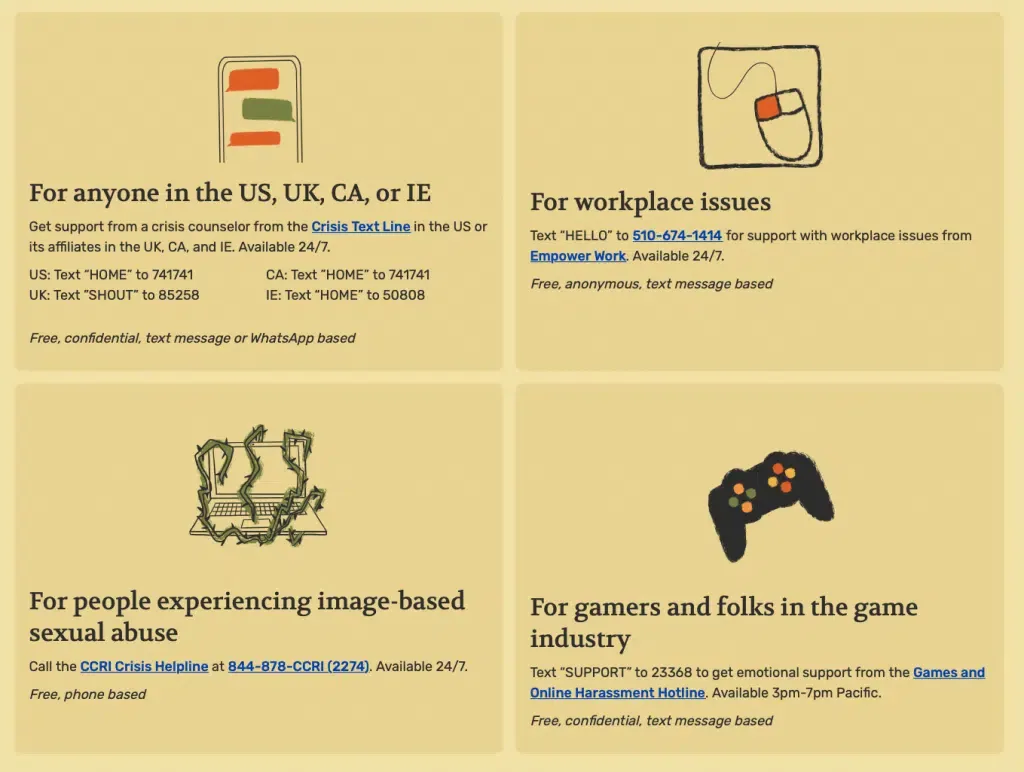
From Tall Poppy’s site, available https://www.tallpoppy.com/resources
In you’re not in immediate crisis, you should always take screenshots and document everything that’s happening. This record can be invaluable during any of the possible process that follow.
There are several in-depth guides available freely online that list resources, apps, and allies available to help you. Here are the ones I’d recommend;
- Online Harassment Field Manual from PEN America
- Speak Up & Stay Safe(r): – A Guide to Protecting Yourself From Online Harassment from Jaclyn Friedman, Anita Sarkeesian, and Renee Bracey Sherman
- Smart Girl’s Guide to Privacy by Violet Blue and published by No Starch Press
- Tally Poppy’s resource page
Each of these will help you understand your options at each step of the way. If you’re not dealing with harassment currently, these are a lot of preventative steps you can take to help reduce your risk.
Take the time to read through these guides and implement their advice.
Learn More
If you’re interested in learning more about these issues and the challenges in addressing them. These links will help;
- Facing the Challenge of Online Harassment , issue explainer by the Electronic Frontier Foundation (EFF)
- You’re Not Powerless in the Face of Online Harassment , essay on Harvard Business Review
- A Handbook for Police and Crown Prosecutors on Criminal Harassment , the Canadian Government’s guide for law enforcement on the issue
- Cyberbullying: What is it and how to stop it , unicef’s explainer for teens which aims at the issue before direct harassment
Researching for this segment was frustrating. Both because of the rate at which online harassment happens and because it’s been hard to find reputable resources specifically for harassment. Especially on the law enforcement side.
There’s a lot out there aimed at cyberbullying education and prevention but not much for adults or about more serious crimes like harassment, hate speech, and direct threats made online.
This issue needs to be discussed out in the open. It impacts our communities and our friends. We need solutions that span technology, law enforcement, social media, and many more areas.
We need solutions that can have a real impact. We’ll only get there if we acknowledge the problem and more forward together.