
The Twitter blue checkmark started as a security control and slowly turned into social status. What happened to the security part?
ChatGPT makes the GPT-3 large language model usable in conversational scenarios. What impact will this have?

Trying to come up to speed on cloud security at AWS re:Invent 2022? Here’s my session guide for attendees of all levels.

CJ Moses, CISO of AWS, delivers a leadership session to highlight the state of security and what’s next.
Highlights from Dr. Werner Vogel’s keynote at AWS re:Invent 2022.

Highlights from Ruba Borno’s AWS Partner keynote at AWS re:Invent 2022.

Highlights from Swami Sivasubramanian’s data and machine learning AWS re:Invent 2022 keynote.

Highlights from AWS re:Invent 2022’s Monday Night Live with Petere DeSantis

Notable new features and functionality announced during day one at AWS re:Invent 2022.

Leading up to AWS re:Invent, these 5 great new features launched to help your cloud security practice.

Mastodon is an open-source federated social media network. Twitter users are flocking to it only to find furstration.

The EU has mandated all smartphones use USB-C to charge by 2024, all laptops by 2026. It’s about time.

Toasters work so well that you forget they need maintenance. If we could get to taht level with cybersecurity controls we’d be lucky…until we weren’t

Your centralized security needs to support a variety of teams building in the cloud…and they all have differing levels of maturity.

The included_files feature of Netlify Functions can be confusing. Here’s how to get it working.

I’ve been publishing to markn.ca for almost 22 years. I broke it yet again in order to fix it.

For stronger security, stop focusing on cybercriminals and pay attention to how your teams are building in the cloud.

If you’ve been harassed online, is there any hope that the criminal will be caught?

The best conference in cloud is back for 2022. Here’s how to get the most out of the show!

AWS re:Inforce brought the people side of security into sharp focus.

Lacework gets named to the Forbes Cloud 100 list for 2022.

Rogers suffered a network outage that took down 35+% of Canadian internet connectivity…whoops?

Compliance is a snoozer of a topic. It shouldn’t be.

The keynote at AWS re:Inforce will send a strong message about security. Here’s what I want to hear from AWS.

AWS uses a very specific session structure for their events. Here is the key to understand the differences.

Visibility is often cited as the top requirement for any cloud security practice…but what is it exactly?

Too often security is a singular focus or area of responsibility. It doesn’t work like that. Security is part of a bigger whole.

Serverless used to mean something…maybe. Does it mean anything to the cloud community today?

The RSA Conference is jam packed with great content. Here’s how you can get the most from your week in San Francisco.

The Shared Responsibility Model provides the roadmap for cloud success. Here’s how to use the model to your advantage.

Machine Learning is a valuable and useful tool…when used correctly. Hear from one of the best how to do just that.

Twitter finally admits it’s working on an edit button. Why now?

Okta is responding to a public cybersecurity incident, what can we learn from how they handled communications?

With cybercriminals becoming bolder, it’s not surprising that we’re seeing more big name breaches.

CloudFlare launches a new API Gateway product, will is shake up the market?

Google Cloud makes some small pricing adjustments and reactions are mixed. Here are my thoughts.

Google Cloud recently cleaned up both the CLIs and SDKs for building in the Google Cloud.
The AWS Audit Manager can help organize all of your audit and compliance evidence. This solution helps streamline the collection of non-AWS resource data points.

The AWS Well-Architected Tool allows users to create their own Custom Lenses. I have thoughts…

Google Chrome OS Flex is going to help put Chrome OS on a lot more computers. That’s a good thing, right?

Kubernetes is challenging to configure and maintain on the best of days. Here’s where to focus your security efforts.
Optimism (an L2 Ethereum project) just paid out a two million dollar bug bounty.

Building a ticketing or registration system? AWS just released a solution to help queue demand.

Attackers can find your cloud misconfigurations with almost no effort, why can’t you?

Once you’ve aggregated all of your AWS Security Hub Findings, here’s one way to visualize and analyze them.

Once you’ve aggregated all of your AWS Security Hub Findings, here’s one way to visualize and analyze them.
Are NFTs, Web3, and Blockchains useful? Or just hype?

Two minutes of work can stop hackers in cold in their tracks.

Bug bounties help bridge the gap between security researchers and companies.

The risks of smart contract bugs are quickly becoming apparently. They can cost millions.

Misconfigurations in Amazon S3 keep happening. Here’s why and how to stop them.

The NFT/Web3 world certain is the wild west…and some projects are way, way more wild.

If you can’t read the code in a Web3 contract, do you really know what it’s going to do?

If a smart contract works as coded and the code is wrong, is the contract valid?

Anytime there’s a security issue, someone gets labelled a hacker. Is that the right term?

Data Privacy Day is upon us once again, here’s an interesting discussion around key privacy topics and how they might impact you.

AWS Security Hub Findings are great, but they can be better. Here’s a simple pattern from the AWS team to enrich those findings automatically.

Here are the steps I use to break down technology topics for a wider audience.

“Um” is not a great call to action, but sometimes it’s all you’ve got.
Can you—as a user—understand an app or service’s security posture? If so, how?

What steps should we take to evaluate the privacy impact of a mobile app?

DevOps and DevSecOps are terms that are thrown around a lot. What do they really mean?

Data Privacy Day is January 28th, can we raise awareness about the issues around data privacy effectively? Will you take action?

5G mid-band is rolling out in the USA with a last minute please from airline industries for more safey precautions. Why the last minute appeal?

Should be able to encrypt your communications? The debate is on…again

A lot of risk decisions are made in the dark…why?

NFTs are digital assets. That means there are cybersecurity concerns with them too.

NFTs are all the rage right now. Make sure you understand what they are before diving in.
The hype around these terms is muddying the waters. What exactly are NFTs, blockchains, and Web3?

Everything in the cloud works on a shared responsibility model. Here’s how it works.
There are a ton of frameworks out there for building solutions but I think conceptually, it really boils down to goals and feedback loops

It’s exciting building solutions with the latest frameworks and technology. Is that the best route to meet our goals? What ARE our goals?

When we talk about privacy, what are we really talking about? The formal definition of privacy is definitely outdated. What would a good definition be?

If the goal of cybersecurity is to make sure that the system you are building works as intended and only as intended, what about stopping hackers?

Security and privacy are inextricably linked. Why aren’t they at the core of all technology?

Log4j is hiding in a number of your systems. Here’s help to plan out your response.

In late 2017, IDT did an AWS “This is My Architecture” video. The video talks about how they managed secret information in their AWS environment.

No one can predict the future. Here’s what the data shows will be trending in cloud security in 2022.

In late 2017, iRobot did an AWS “This is My Architecture” video. The video talks about how they deployed their microservices in AWS.

Every year AWS sets the tone for all of cloud at AWS re:Invent. Here’s what you can expect in cloud computing for 2022.

The leadership session at AWS re:Invent provide a deeper dive into a specific area of focus. Stephen Schmidt, CISO at AWS takes the stage to talk all things security.

AWS re:Invent is always THE event in cloud. Werner Voegls delivered the latest version of his hotly anticipated keynote on day four.

Amazon Inspector first launched in 2015. Now in 2021, it’s re-launching with a brand new architecture and a host of new features.

AWS re:Invent is always THE event in cloud. Petere DeSantis’ keynote provided a peek behind the curtain of the technology that drive AWS itself.

Corey Quinn interviews key AWS leaders in a casual settings. This time he sits down with Bill Vass, VP Technology & Engineering

AWS re:Invent is always THE event in cloud. Swami Sivasubramanian took the stage to deliver the machine learning focused keynote on day three.

AWS re:Invent is always THE event in cloud. Adam Selipsky gave his first keynote as the CEO of AWS. Here’s what he covered during this two hour session.

Amazon Inspector first launched in 2015. Now in 2021, it’s re-launching with a brand new architecture and a host of new features.
AWS re-launches a dramatically improved Amazon Inspector, a software vulnerability discovery/management service.

Here are the top AWS announcements leading up to and during AWS re:Invent 2021.

AWS re:Invent is always THE event in cloud. This post is the ultimate guide to getting the most out of the show.

AWS re:Invent is always THE event in cloud. This year a lot of people can’t attend in person. This post tells you how to get the most out of the virtual side of the event.

AWS re:Invent has over 500 sessions available remotely. Here’s a near complete list for easy searching.

An overview of the AWS Well-Architected Frameworks’ Performance Efficiency pillar.

Most security practices make the same set of mistakes when moving to the cloud. This talk looks at those mistakes and how to avoid them.

An overview of the AWS Well-Architected Frameworks’ Reliability pillar.

There are massive opportunities to advance your security practice as your business moves into the cloud. This talk provides a step-by-step approach that will help you maximize them.

An overview of the AWS Well-Architected Frameworks’ Cost Optimization pillar.

An overview of the AWS Well-Architected Frameworks’ Security pillar.

An overview of the AWS Well-Architected Frameworks’ Operational Excellence pillar.

In late 2017, Airbnb did an AWS “This is My Architecture” video. The video talks about how they built a system to test their Amazon RDS databases.
AWS Labs has a lot of open source code up on GitHub. This repo helps you visualize your AWS workloads and highlight areas of cost.
AWS Labs has a lot of open source code up on GitHub. AWS Data Wrangler is a bridge between python pandas DataFrames and AWS data services.

AWS Labs has a lot of open source code up on GitHub. This repo provides an easy way for developers to view your Amazon API Gateway APIs.
AWS Labs has a lot of open source code up on GitHub. This repo helps you visualize your AWS workloads and highlight areas of cost.
AWS Labs has a lot of open source code up on GitHub. This repo helps you visualize your AWS workloads and highlight areas of cost.
AWS Labs has a lot of open source code up on GitHub. The code in this repo lets your embed Amazon QuickSight dashboards in your HTML.
AWS Labs has a lot of open source code up on GitHub. This repo contains a solid set of AWS WAF rules for common web-based attacks.
AWS Labs has a lot of open source code up on GitHub. Gluon TS helps you create forecast models for time series data.

AWS re:Invent is always THE event in cloud. As 2021 draws to a close, what path will AWS set the cloud on. What new services, features, and tools will builders get to create with?
AWS Labs has a lot of open source code up on GitHub. This post looks at the AWS Lambda Powertools for Python.

In late 2017, Station X did an AWS “This is My Architecture” video. The video talks about how they built out a genomics processing pipeline on AWS.

AWS Labs has a lot of open source code up on GitHub. This post looks at the AWS Deployment Framework.
The Amazon Builder’s Library is a great set of deep dive papers into the challenges with modern systems. This post looks at how Amazon balances system stability between control and data plane requests.
The Amazon Builder’s Library is a great set of deep dive papers into the challenges with modern systems. This post looks at how Amazon conducts hands-off deployments.

DevSecOps is the latest in a long line of buzzwords. The core makes sense: work on security earlier. But why isn’t this everywhere? Here’s the biggest mistakes teams are making trying to “do” DevSecOps.
The Amazon Builder’s Library is a great set of deep dive papers into the challenges with modern systems. This post highlights some of the challenges in dealing with multi-tenant systems.
The Amazon Builder’s Library is a great set of deep dive papers into the challenges with modern systems. This post highlights some of the challenges that the retry pattern presents.

In late 2017, Capital One did an AWS “This is My Architecture” video. The video talks about how they built Cloud Custodian and how that tool helps them enforce policies in the AWS Cloud.

The Amazon Builder’s Library is a great set of deep dive papers into the challenges with modern systems. This post highlights some of the challenges in dealing with failure at scale.
AWS has a huge library of fantastic resources. This post highlights the recently released whitepaper walking public sector organizations through machine learning best practices
AWS has a huge library of fantastic resources. This post highlights the recently released whitepaper talking about serverless multi-tier architectures.
AWS has a huge library of fantastic resources. This post highlights the recently updated whitepaper aligning the NIST Cybersecurity Framework to AWS.
AWS has a huge library of fantastic resources. This post highlights the recently released whitepaper about building reactive systems on AWS.

In late 2017, New Relic did an AWS “This is My Architecture” video. The video talks about how they setup their Terraform execution plans in a modular fashion. This provided the team some much needed flexibility when managing builds.
AWS has a huge library of fantastic resources. This post highlights the recently updated whitepaper on building out a CI/CD practice in the AWS Cloud.

Are you a security professional or a builder looking to learn more about security? This year, I wrote the official guide for security attendees to AWS re:Invent. Here’s what’s in it and why.

AWS re:Invent is always THE event in cloud. As 2021 draws to a close, what path will AWS set the cloud on. What new services, features, and tools will builders get to create with?

In late 2017, CorpInfo did an AWS “This is My Architecture” video. The video walks through how they handled a massive amount of events coming from various IoT devices they had deployed. Remember, this was before any of the AWS IoT-specific services!

Facebook commits $10B per year to build the multiverse. Earnest attempt at progress or an attempt to divert attention?
Passwords suck. Why are we forced to follow these weird rules. Do they really keep us safe? Here is a solid way to safely handle all of your passwords.

In late 2017, Civitas Learning did an AWS “This is My Architecture” video. It was one of the first. The video walks through how they handled processing personally identifiable information at scale using batch processing.

In late 2017, the Finanical Times wanted to get developers to factor in cost to their designs. They created a gamified solution to help drive this change…and it worked.

We’re producing more audio and video than ever. But you can’t get the most out of that content until you transcribe it to text. In this stream we do that using the Google Cloud.

Twitch has been hit by a major data breach. 165GB of critical information was leaked on 4chan. What will the impact be? Will this cause even more streamers to leave?

In late 2017, Netflix explained how they tackled the problem of failing over when disaster struck. Four years later, how well does that design hold up? What could we improve given the services and features available today?

Facebook, Instagram, and WhatsApp are deeply integrating into many aspects of daily life for many communities and business. One networking misconfiguration reminded 3.5 billion users of just that.

In late 2016, Lyft demonstrated the service discovery engine they built on AWS. Five years later, how well does that design hold up? What could we improve given the services and features available today?

On my tech column with CBC Ottawa Morning, Dr. Tracy Valliancourt and I explain the challenges with Instagram Kids and the latest research from Facebook about its impact on teens.

Live Text is now available in iOS and iPad OS but not macOS. I try to fix that with the help of Google Cloud in this tiny cloud project.
Misconfigurations are the number one security concern in the cloud. Guardrails can help you prevent misconfigurations from happening. This talk shows you the principles behind sustainable, useful guardrails.

There are a lot of acronyms related to cloud security. What do they mean and can they help you?

As a new user in the AWS Cloud, is AWS App Runner the service that’ll get your one container up and running quickly? This post explores that question.

As a new user in the AWS Cloud, what does it take to get one container up and running? What service do you user? How many steps are there? This post explores that question.

The second installment of AWS re:Inforce was entirely virtual and gave a great view of the state of security in the AWS Cloud. Here’s what the event says security practices and how to set yours up for success.

AWS re:Inforce returns in person and provides a deeper look into how AWS views security.

The Microsoft Edge browser team is conducting an experiment in an attempt to increase the cybersecurity of the browser and how it handles javascript. At stake? One of the major performance features.

A new report from a United States Senate Committee gave 24 US department and agencies an average grade of C- in cybersecurity. That’s not good.

The region of Lazio was hit by a ransomware attack and is struggling to recover from this attack on critical infrastructure. BlackMatter, a new ransomware supergroup, just announced they wouldn’t conduct these types of attacks. What does it mean for the future of ransomware?

EA got hacked and 780 GB of source code was stolen. The hackers attempted to extort EA and when they didn’t pay, the data was dumped online.

The US government takes steps to codify cybersecurity requirements for critical infrastructre.

Twitter’s latest transparency report shows a low uptake for the multi-factor authentication feature. This is a great security control that’s easy to use. What’s going on?

The Pegasus Project is a collaborative effort by a number of media and advocacy organizations around to the world. With their work, they are shining a light on nation state use a specific malware tool: Pegasus spyware.

There are now 5 seniors leaders in the US federal governments with cybersecurity as their primary mandate. Is this going to be a problem?

Two new resources launched to help people understand the challenges associated with ransomware; StopRansomware.gov and RansomWhe.re

Are security agent programs bad? Don’t even answer, that’s a ridiculous question.

REvil has been one of the top ransomware groups for the past few months but they’re suddenly offline. No note, no warning, just gone.

Long after the headlines pass, victims of ransomware are left struggling to get back to “normal” operations. It’s a long, challenging road back.
The out-of-band patch for PrinterNightmare on Microsoft Windows doesn’t completely fix the issue. What are IT and security teams to do?
The REvil gang attack Kaseya, an IT management platform, and that got them access to 800—1,500 more businesses without any additional effort setting the new normal.

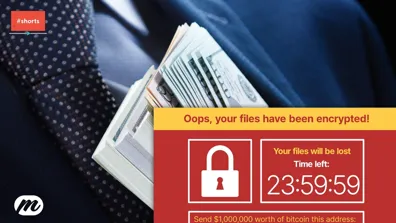
Ransomware is absolutely everywhere. What is going on? Why is ransomware so effective? Is there anything we can do about it?

Criminals are using real apps they’ve made and a push to remove ads to harvest Facebook credentials in order to gain more personal information to sell.

PrinterNightmare is a high severity vulnerability that affects all versions of Windows and is being actively exploited…on a long weekend 😬
Microsoft Windows 11 will require a Trusted Platform Module (TPM) on all PCs. Will this long-needed requirement help or hinder?
Some WD My Book Live users had a shock this week as hackers remotely wiped their data. What can they do about it?

Apple is under fire on a number of fronts. The biggest issue this week is several bills introduced in the US. A key issue? The ability to “sideload” apps on your iPhone.

When your local electric utility offered a new smart thermostat a heavy discount, a lot of homeowners jumped at the chance. Unfortunately, a clause in the terms of the promotion grants the utility access to your data and the ability to remotely control the device!

Apples annual developer conference announced the latest version of all of Apples operating sytems and privacy was a key pillar across all of them.
Apple and Facebook have been battling very publicly around privacy issues. What’s really going on?

A discussion about the evolution of security in the cloud. Security is now becoming a critical piece of a developer’s pipeline, what does that actually mean?
Celebrating three years of the CISO/Security Vendore Relationship Podcast

A purely digital RSAC 2021 kicks off looking back at a challenging year and to the challenges ahead for the security community.

In software, developers often don’t have a choice. Speed becomes a business imperative for survival and to stay competitive.
An all virtual RSAC 2021 kicked off today. What are the themes? What do we expected to see? This discussion on theCube has you covered.

Colonial Pipeline is recovering from a ransomware cyberattack. There’s a ton of attention on them right now, what do you need to know about this issue?
AWS IAM has been going strong for 10 years! To celebrate the anniversay, this four part series by various AWS Heroes, highlights some key features of the service

The AWS Identity and Access Management (IAM) service turns 10 years old today. While it’s a fantastic service that keeps adding features, it really was the first step towards real cloud security.

I recently made a career move and it’s allowed me to re-double my efforts in the community. What do you want to learn about cloud and security?
Google continues to advocate for a ‘privacy-first’ web. The problem? Their definition of privacy and how it seems to be a Google-powered adtech nightmare.
iOS 14.5 introduces App Tracking Transparency or ATT. Here’s what it means to you.

No other technology revolution has induced more fear, uncertainty, and doubt for so long than the cloud. This post explores the “why” of it and more…

It’s hard to keep track of all of the amazing content on the web. To help, I’ve created a few “super feeds” for your favourite RSS reader.

Ubiquiti suffered a data breach and makes it worse by not communication clearly with it’s customer base.

Google has had to disclose the amount of tracking its apps do in iOS. Shocking no one: it turns out it’s a lot.

iOS 14.4.2 fixes a critical cybersecurity issue. Make sure to update now.

Setting a new cloud account well is reasonably simple, but what about accounts that are already active? Here are some tips to add guardrails after the fact.

iOS 14.4.1 fixes a couple of critical cybersecurity issues. Make sure to update now.

Clubhouse is the hot new social network. It’s a promising audio-only network that now boasts over 2 millions active weekly users. During this rise, it’s committed some easily avoidable and obvious mistakes around privacy and content moderation. Can they recover?

Security and privacy are linked yet for some reason, you see privacy experts ignoring the impact of security and security experts who are unconcerned with privacy. Why?

Emotet and NetWalker are both taken offline within days of each. A big wins for users, law enforcement, and international cooperation…at least for a little while.
Parler gets deplatformed and can’t find any organizations that want to work with it. It’s about time.

Week three of three (!) for AWS re:Invent 2020 kicks off and this post will be my “live blog” for the week. Check back often for reactions, news, and tips on how to get the most out of the week.

There’s always more than one way to solve a problem. That’s a big advantage of AWS, but it can also be overwhelming to deal with. You will make mistakes. That’s ok.

Week two of three for AWS re:Invent 2020 kicks off and this post will be my “live blog” for the week. It will be neither “live” not probably completed this week. Check back often for reactions, news, and tips on how to get the most out of the week.

Amazon EventBridge helps build loosely coupled applications that scale independently and makes it easier to integrate cloud-based applications and services.
As you continually evolve your use of AWS products and services, it’s important to consider ways to improve your security posture and take advantage of new security services and features. This session shares architectural patterns for meeting common challenges, service quotas, and tips and tricks for continually evaluating your architecture against …
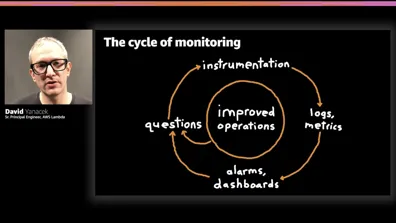
To operate services, Amazon relies on having high-fidelity visibility into how its systems behave and the user experience, whether that’s using AWS services or shopping on Amazon.com. In this session, learn about Amazon’s never-ending journey for the perfect granularity of monitoring. This session covers the full spectrum of monitoring at Amazon, …

On my tech column with CBC Ottawa Morning, I explain how politicians are using the online game, Among Us, as a platform to reach younger audiences.
Coverage of the keynote of AWS re:Invent 2020 where Andy Jassy delivers new services, features, and more.

Week one of three for AWS re:Invent 2020 kicks off and this post will be my “live blog” for the week. Check back often for reactions, news, and tips on how to get the most out of the week.
AWS re:Invent is always jam packed with new content. This post is a road map for my content during this three week virtual event.
Passwords are the worst. Trying to pick a “secure” one makes the whole thing worse. Every site and service has it’s own variation on the “rules” for making a strong password and it’s hard to remember what you’ve set your password to.
Are those rules really making our passwords stronger? Do we need so many …

AWS launches a mountain of new features leading up to and during AWS re:Invent. Here’s the list of announcements for 2020 and my perspective on a lot of them that I think will help you build better.

MFA is one of the most powerful tools a user has to protect their accounts
Apple recently launched macOS Big Sur and a security researcher’s post vent viral highlighting a steady stream of communications that “phone home” detailing what apps you’re using on your system. What’s going on here?
Is privacy promoting Apple actually spying on every app running on every macOS system around the …

Apple has launched the first MacBooks and Mac Mini using custom Apple Silicon. What does this mean for the future of your computer?

AWS re:Invent is the best conference in cloud. This post lays out what you need to know to get the most out of the 2020 edition of this amazing event.

Is your day chalk full of video calls? Wondering why you’re exhausted at the end of the day? The two might be related 😉. In this column, Robyn and I discuss some of the reasons for ‘zoom fatigue’ and what technology might help address it.
Ad-tech, digital marketing, and the surveillance economy are worth billions and billions of dollars. It all hinges on the ability to target ads and you can’t target ads without tracking users and their devices.
A privacy-focused design decision by Apple for iOS 14 puts Facebook on edge and Google on notice. What is the IDFA? What happens in …

Epic Games is current waging war on Apple and Google over the right to distribute apps to mobile users. There’s been a ton of excellent coverage of the issues, but it’s usually missing one key perspective; what do we as users get from the App Stores?

The Canada Revenue Agency suffered a large breach exposing over 5,000 citizens to COVID-19 benefit fraud. This issue exposes some of the challenges of providing authentication services to millions of citizens. Why did this happen? And what can we do to protect ourselves?

On July 15th, 2020, Twitter was hit with the most visible hack of a social network of all time. 130 of the top accounts tweeted out a bitcoin scam. A month after, have we learned anything? What’s the impact of continuing to use Twitter?

Outages are hard to handle. There’s pressure to get things back up and running, to avoid damage to your reputation, and to avoid getting yelled at by the boss. The Help Desk is often the best positioned team to help…and the most overlooked. Here are some tips to help handle the communications side of incidents better.

The President has promised to ban TikTok in the United States for national security reasons. Is that the case? Are there real security & privacy concerns or is this purely a political move?

AWS re:Invent is the best conference in cloud. This year it’s an entirely virtual experience spread over 3 weeks. This post will help you get the most of out the event. (Updates regularly)

Is a social network focused on dancing, lip syncing, and fun a threat to national security just because of who owns it? Is TikTok a threat to national security? Do you need to worry about it you or your family using it?

🗑🔥 doesn’t quite cut it anymore. Following a random thought, I dive into the process to create a new official emoji and why isn’t ‘dumpster fire’ in the official list?

The Well-Architected Framework is a set of principles that can help you find the ideal build for the problem at hand…regardless of the size of that problem. This post walks you through the application of the framework to a small problem but delivers big returns.

#BlackLivesMatter has risen to prominence again in the past weeks as protests spread beyond the USA to the world. A positive shift is happening as anti-racism is taking hold in privileged communities. This is a challenging subject and one that can be difficult to address with your family. Here’s a set of resources that I’ve found …

Is working from home the new normal in tech? Is working from home as simple as ensuring a strong internet connection and access to the right tools? This is an issue with a ton of impacts outside of just the relationships on your team. This post highlights various conversations and points of view on the issue.

The Unicorn Project is the latest book from Gene Kim, one of the leaders of the DevOps movement. The book focuses on developer enablement and culture. What does this have to do with cloud security? Everything.
The cloud is an amplifier. It lets teams do more with less. This innovative and fast-paced approach creates a mountain of security …

We’re all stuck inside and it can quickly feel like you’re drowning in possibilities for technology that will help you work, learn, and stay in touch with your community. How do you make any of it work? How do you move forward? In this hour long call-in show, Rita Celli and I try to throw you a life preserver.

The second series of my live streaming series for Trend Micro. In it,I speak to various cloud leaders about what’s happening in cloud.

Presenting on video and live streams is hard. Even though the goal is to connect to people, sitting alone(ish) presenting to a camera lens and computer display can be alienating. There are a number of simple techniques you can use to upgrade the quality of your present and stream. This post walks you through planning out and delivering a high …

Video conferencing platform Zoom has been in the news almost constantly over the past few weeks. At first it was hailed as a tool to help reduce this isolated feeling all of us are experiencing, then it was a pile on for security and privacy issues, and finally the last two weeks have started a redemption story.
Security is often spoken of in absolutes. Is this secure? Is that insecure? The reality is that security is a spectrum. It is a series of implicit and explicit decisions made to meet the business needs within an acceptable risk tolerance.
What is an acceptable risk? How can you determine what threats pose a risk to your work? How likely are those …

Contact tracing during an outbreak is a massive undertaking. Google and Apple are collaborating in order to automate parts of this task. Will it work? What are the challenges? We dive into the issue

A Cloud Guru is hosting Cloud Madness. Thirty two cloud services face-off over four rounds but only one will be crowned the champion. Here’s my completed bracket and reasonable for my picks.

Are you addicted to your smartphone? How would you know? Is there anything you can do about it? Over the course of an hour, Rita Celi and I asked people from around Ontario questions about the issue

CES 2020 brought out the big (and small) players in tech and one thing they all had in common was how much they used the word “privacy”. Is this privacy-washing or the start of real change?
COPPA was passed in the US in 1998 but a recent ruling against YouTube for violating the decades old law means big changes for creators.

Canadian data privacy laws state that an organization is responsible for the life cycle of the data. Most orgs struggle with protecting it while it’s in use, what about after they no longer need it?

In this live streaming series for Trend Micro, I speak to various cloud leaders about what’s happening in cloud.

AWS re:Invent is the biggest and most exciting conference in cloud. Follow AWS Community Hero @marknca for all of the latest leading up to and during the show!

Organizations struggle with extending their security practices to the cloud. Traditional approaches don’t work, and new cloud-only practices duplicate work for an already overtaxed team. The goal of cybersecurity is simple: to ensure that what you build works as intended and only as intended. This session teaches you how the AWS Cloud Adoption …

Black Friday and Cybermonday are two of the biggest shopping days of the year. Consumers rush to get the biggest deals on all sorts of items. Sadly, scammers and cybercriminals also rush to take advantage.

AWS has recently explored with great machine learning services. From the core building blocks to services design to teach you techniques to simple transactional services that just get the job done. This stream looks provides an overview of these services and when you might want to use them.
Canadian data privacy laws state that an organization is responsible for the life cycle of the data. Most orgs struggle with protecting it while it’s in use, what about after they no longer need it?

AWS offers a number of services it labels as “compute”. What are they? How do you pick one that makes sense for your workload? How are they different from each other? This live stream tackles these questions as we take a look at computation in the AWS Cloud.

Technology is omnipresent in our lives. From the time you wake up and check the weather to the time your head hits the pillow, you will have spent at least a quarter of your day interacting with technology. In this talk, Mark Nunnikhoven, vice president of Cloud Research of Trend Micro, will navigate you through your average 24 hours and uncover …

Google really doesn’t like humans and they LOVE data. At the intersection of those two areas is a new A.I assistant that calls business to complete simple tasks for it’s users and to automatically update Google’s databases: enter Google Duplex.

Amazon DynamoDB is an exciting database services. It’s a cloud-native, NoSQL offering that is lightning quick and scales seamlessly. However, if you treat it like a traditional RDBMS, you’re not going to see any of those benefits. In this live stream, I explore some mistakes I’ve made and how to fix them by moving to a …

AWS offers a wide range of databases but making sense of these services can be tricky. In this live stream, we explore these data services and why you pick one over another.
Getting users to accept new security controls is an uphill battle, any setback makes it harder for any solution to push out additional security measures. Remember that security features are just like any others. They will be triaged for bugs and prioritized according to criticality and demand. And sometimes, other pressures mean that the …

Mistakes happen. Even after taking steps to restrict permissions and setup systems, builders will make misconfigurations and mistakes. This stream presents two different approaches to catch those mistakes before they come back to haunt you.

AWS re:Invent is absolutely massive. The only way to keep things somewhat organized is to use a reserved seating system for sessions. That system opened today and I live streamed the ins and outs of booking seats for various events.

Serverless architectures help you and your team focus almost entirely on delivering business value. They also break almost every existing security technique. I’ve been actively researching serverless security for a while now, here’s what I’ve learned over the past three years.

Cybersecurity is topic that comes up regularly as something you have to do…or should do…or are forced to look at by your security team. But why? There have been reports of serverless threats. Rumours of traditional security issues that should keep you up at night. Is any of it real?
When new technologies are adopted, cybersecurity implementations …

Serverless is hot right now, but are we all talking about the same thing? In this live stream, we dive into what serverless is, why it’s a big win for your business, and how to get started.

Security is often misunderstood and addressed in the last stages of a build. Operationally, it’s ignored until there is an emergency. In this talk, we review several advanced security processes and discuss how too easily automate them using common tools in the AWS Cloud.
This approach helps you and your team increase the security of your build …

Amazon Athena lets you treat files in Amazon S3 like they were a database. That doesn’t sound too cool until you realize the possibilities: data stays in place, storage is low cost, data management gets easier. Now add in Amazon Quicksight. This service allows you to quick and easily visualize that data and share your insights. This one-two …

Amazon S3 was one of the first AWS services and it continues to be the cornerstone of the AWS Cloud today. This stream covers the basics of the service and how to ensure that your data is only accessed in the ways that you expect.

CBC’s Go Public pointed out the rising rates of e-transfer fraud and consumers are shocking. The expectation was that e-transfers were safe and convenient…turns out, not so much.

Keeping a personal website up to date is always tricky. The technical pieces are simple, it’s be satisfied with the design and making the commitment to focus on the site when there is a ton of other, maybe more interesting work to be done. Needless to say, this is my restarting this site!

The Shared Responsibility Model governs how operations (which security is a part of) work in the cloud. In this live stream, we explore the realities of the model and how to verify AWS is fulfilling their responsibilities.

Don’t be afraid of the command line (CLI), it’s insanely useful. This live stream explores those uses and shows you how to use the AWS CLI to accomplish some simple but helpful tasks in the AWS Cloud.

AWS Lambda is probably the most talked about service in the entire AWS Cloud. It lets you run your code based on various triggers with almost no overhead. In this live stream, we look at AWS Lambda basics and even complete a small project connecting code to events in S3.

AWS re:Invent 2019 is going to be HUGE. Mark will be conducting a series of live streams and publishing a ton of content leading up to the show in early December. In this stream, we get the series started off with some questions to you and an overview of what to expect.

CBC News posted an article about how Canadian federal MPs are using digital tracking technologies on their personal websites. So what is retargeting? How is it used? Why is its use in politics different?

Letting customers know about a security vulnerability is never an easy thing. From the logistics of it to the reputation management issues. But this is a critical aspect of delivery software and services. What’s the best way to tackle this problem?

Cybercriminals don’t always use complicated technical attacks to get around your cybersecurity. Sometimes—probably more often than we care to admit—it’s the really simple stuff that works and what’s simpler than an email?

Facebook was recently called out for listening to users audio messages on Facebook Messenger. They aren’t alone. Apple, Amazon, Google, and Microsoft all have admitted to having contractors analyze audio from their voice assitants (and Microsoft’s Skype service). What’s the impact? Do you need to worry?

NULL is one of many special characters that has a long history in computing. What are the consequences of using NULL as a value provided via user input. The easy answer should be “nothing” but reality is a lot messier. Joseph Tataro set out to get a nerdy license plate and found out just how far the rabbit hole might go…

FaceApp (first released in 2017) is back in the news for the #AgeChallenge and a host of privacy concerns. There’s a lot of knee-jerk reactions around the app but what’s really going on? We dive in on this (as usual) no-BS episode…

Recently on Twitter a nerd fight started around the idea of a 10x engineer. VC Shekhar Kirani kicked things off by advocating that startups do anything to grab these types of employees. Needless to say, a lot of differing opinions were shared on the matter. It’s an interesting topic and one we dive into on the show today.

Zoom.us had a pretty egregious security issue this week. Their response was poor despite the best efforts for responsible disclosure by the security research who discovered the issue. While this issue has dominated tech headlines, the real issue is much more significant and commonplace.

Cybercriminals don’t always use complicated technical attacks to get around your cybersecurity. Sometimes—probably more often than we care to admit—it’s the really simple stuff that works and what’s simpler than an email?

A quick update on why MwM has been missing the past couple of weeks and where this show is going in the future.

Recently a video of mine was flagged by YouTube’s automated ContentID system which may or may not have been justified. Regardless, it got me thinking of the mismatch in motivations for builders investing in cybersecurity and privacy.
What are those motivators?
At Apple’s Worldwide Developer Conference (WWDC), Apple made several announcements that focus on user privacy. In this episode, we’ll explore these features and what impact they may have on you.

On Kara Swisher’s show, Recode Decode, she recently hosted Gabe Weinberg from DuckDuckGo. Their conversation revolved around some core concepts in online privacy.
During that conversation, a few terms popped up that I think are often misunderstood or misinterpreted. This episode looks at those terms and what they actually mean.

Bad Robot Transcript Good morning on this episode of the show. We’re going to take a look at the recent moves by nest and how they impact your privacy. The Nest Labs was founded in 2010 and quickly Brought The Nest learning thermostat to Market. This iconic product was a transformative product for the smart home. You see it everywhere. …

Huawei was recently put on the US Entity List from the US Department of Commerce. That essentially means that it needs a license to receive technology from US companies…a license that is a default “no” and in this political climate, a definite “no”.
Politics aside, what does that mean for Huawei smartphone users?
The Digital Economy Act of 2017 in the UK is trying to put up enforceable age gates to pornography. That might be a good idea but it’s extremely difficult to actual do online. At the same time, here in Canada, our major financial players are launching a joint identity service.
Connect both of these issues together and the larger issue …

A recent CBC News article highlighted both the powers of border agents to search digital devices and the general lack of awareness of your rights at the border. Are you aware of your rights as you cross the border? Do you take precautions to protect your digital footprint?

Facebook held its annual F8 developer conference this week and—in addition to the usual product updates—they repeatedly talked about creating and enabling private spaces. What’s stopping them? 15 years of poor information management.

The NBA playoffs are in full swing and there’s a huge rules controversy around one superstar’s—James Harden—jump shot. Is it a foul? Regardless of the answer, it pushes the rules to the limit. The same thing happens in cybersecurity. People just trying to get their job done will push the rules to the breaking point…and sometimes …

AWS re:Invent is the best conference in cloud. This post lays out what you need to know to get the most out of the 2019 edition of this amazing event.

The Fortnite developer teams at Epic Games are working in a perpetual “crunch time” situation. That’s not sustainable by any measure…and from all reports, things are bad over at Epic.
But they are not alone. How does this time crunch impact the cybersecurity community?

Facial recognition is becoming more and more common. In some cases, it’s used to make existing procedures more efficient or to connect existing data points together. While that seems like the community has already consented to these use cases, people often have a visceral reaction to hearing that new technology is being applied.
Since May of 2016 Facebook has been prompting some new users for their email passwords. Yes, their email passwords. WTF?

Thomas Brewster, writing for Forbes, highlighted a recent case by the DEA. The case itself isn’t out of the ordinary. What is interesting is the issues raised by search warrant request for LogMeIn.com…parent company of LastPass. This password management service is used by the accused and is potentially a treasure trove of information …

It’s tempting to search for the perfect solution to a problem. The challenge? That “perfection” rarely exists. But time after time, we seek out these perfect solutions. Nothing’s perfect. Security is far from perfect. But we keep trying for perfect sceurity…why?
Serverless architectures are a fantastic solution to a lot—not all—design challenge. The benefits they bring are substantial and they can reduce the overall ops and development burden for a lot of teams. But when we’re talking about serverless, are we all talking about the same thing?

A recent report from the Canadian Commission for Complaints for Telecom-television Services (CCTS) saw a dramatic increase in complaints with billing being one of the top reasons. That’s not especially noteworthy in an industry known for poor customer service…until you dig a little deeper.

A recent study by NCSU found that there are way more API keys and tokens uploaded to GitHub than previously thought. In fact, there’s almost a near constant stream of secrets being exposed…why?!?

Google recently announced a new, all-in-the-cloud gaming service called Stadia. For gaming fans, there’s a lot of potential that—fingers crossed—hopefully pans out.
But the design of the system is an implementation of a pattern we use in securing high sensitivity data as well.
Has this pattern’s time finally arrived?
An interesting op-ed from Dr. Egginton at John Hopkins University highlights some efforts underway in the US to declare learning to code the equivalent of learning a new language.
Both are important but will they help your cybersecurity career?

A recent survey from RightScale showed a lot of confusion around cloud computing costs. The common take away? Organizations are surprised at how high their cloud bills are. Similarly, the community was surprised at the size of Lyft’s commitment to AWS (around 8 million per month).
But the root of this problem isn’t what you think.

A recent tweet called out a user’s perception about Grammarly, a SaaS-based grammar and writing tool. They accused the service of being predatory (due to it’s license) and a keylogger. While the points are off base (but not insanely so), they do raise a bigger issue: the user perception about a service vs the actual privacy risk

I you were just starting to try and understand the cybersecurity problem space, a CEO or CIO working to better grasp the challenges facing your organization, how would the industry look? Would you be able to spend wisely? To make decisions taht would actually improve the security of your organization? My view from RSA 2019 in San Francisco

We rely on some digital services for critical functions around security and privacy. Trusting those services is paramount to their success and ours. But it can be difficult to trust when you don’t know what’s going on behind the scenes. Gag orders from the courts can amplify those trust issues. The idea of a warrant canary can help to …
Websites, apps, and even your desktop applications may be tracking a how lot more of your behaviour than you think. The reason in most cases is simply to deliver a better application from a technical perspective. But sometimes, it’s more insidious.

You’re building out a digital identity for you kids almost from the day they are born. But it’s not just you, the clubs they belong to, schools they attend, and sports they play are all contributing. What’s the impact to your child? To their digital future?
There has been a significant increase in DNS hijacking attacks over the past couple of months…and why not? It’s a simple, direct way for cybercriminals to take over an organizations identity or to intercept critical communications.

You agree to new contracts all the time but you probably don’t think of them as contracts, they are simply the “Terms of Service”. A recent study found that most of these agreements are essentially unreadable. That sets up a one-sides relationship between the services and their users. Fine for the services, not so much for the …

Cybersecurity is a major topic when it comes to modern elections. With Canada probably going to the polls in the fall, discussion is heating up about the potential impact of cybersecurity this election cycle. The good news? Canada’s election infrastructure is well protected. The challenge will be with various political parties and their …

Security research can be a tricky thing. Depending on where you are and what jurisdiction you fall under, the research you conduct may be illegal. That can give companies who are resistant to outside researchers the ammo they need to strong arm research teams. What’s the best way forward?

Cryptocurrencies have dropped in popularity and value but cybercriminals continue undeterred. The latest on cybercrime and cryptocurrency…
Facebook continues to do anything they can to build data profiles on users. This week it was revealed that they shifted their Onavo efforts to a new “research” project where they targeted 13-35 year olds via 3rd party market research companies. Lots of questions and issues here…

GDPR has been in effect for a few months and we’re starting to see the first major rulings. Google was just hit with a 50m Euro fine for not being clear enough in their intentions with user data. Is this a turning point? While regulation and legislation is typically followed to the letter, there are a lot of areas of GDPR that have specific …

The 10 Year Challenge is sweeping social media right now. It’s a harmless way of looking back at yourself—and everyone else—a decade ago…or is it?
Is there something more to this challenge? Something very big brother tied to facial recognition?

Network security is struggling to keep up with the reality of how organizations are build and connect today. From hybrid network (on-premises and in the cloud) to large mobile user bases, traditional network security—push everything through a choke point—is well past it’s best before date. What’s next?

It’s not uncommon for cybercriminals to combine multiple data sets in order to increase their chances of finding valid user credentials. Security researcher Troy Hunt found the mother of all collections, dubbed “Collection #1”. This roll up contains 773M sets of credentials from various breaches.
But why does this work for …

Data is extremely valuable. We’ve seen that with data brokers, social media giants, and almost every company out there. The current attitude is to gather all the data possible, save it forever, and monetize it later on.
That’s problematic for a number of reasons.
Three articles this week each touching on smartphone data highlight a much bigger issue. Each of these articles remind us how much data our phones generate and how valuable that data is. Yet we don’t treat that data as valuable. It’s packaged and resold with no compensation to the owner of that data…if they are even aware that …

2019 is in full effect and I’m stumbling?!?
Planning for a new year is exciting but can also be challenging. When I sat down to plan out 2019 vlogging and what topics to handle around security and privacy, I see a massive opportunity.
But that opportunity can be challenging to break down into manageable pieces…

150th episode! As I wind down for the year, I always try to look back at what has worked and what hasn’t. This show has evolved from a simple “get some ideas out there” to a regular view on how security privacy impacts our technology and our communities.
Names matter. They help a community come together around a singular concepts. But what happens when definitions and usage differ?

Sometimes things don’t go as expected. That can be frustrating and unfortunate…but also an opportunity to learn.

How much can one jurisdiction affect the internet? Turns out, a lot. Recent actions by the US and Australia are having and could have a disproportionate impact on our online communities.

Security metrics are hard. But that doesn’t mean you should ignore them. In fact, a lot of teams are measuring the WRONG things which leads them down a path where efforts are being spent in areas that aren’t driving to their bigger goals.

Fortnite is an international sensation. Despite being truly free-to-play, they are making a lot of money by continually improving the game experience, balancing the in-game economics, and other critical factors.
There is a ton to learn here about delivering a service. Security and IT teams really should look to this type of service in order to …

Data privacy is a critical area of concern around the world. Look no further than four distinct events today: Australia passing a new law, an arrest for Huawei, Apple publishes a new paper, and the Government of Canada sets a new directive.

After a jam packed AWS re:Invent 2018, I’ve been thinking about how to deliver information to an audience. One of the challenges is delivering that information with enough context that it makes sense to that audience.

When you are trying to get a message out to a lot of people, it’s not realistic to try and get them all back to you digital properties. So what do you do? How do you manage trying to hold the same conversations in multiple places? How do you monitor what’s working?

The “secret” to most success is being prepared. Taking a few minutes or hours to map out what you want to happen is far better than trying to figure it out when you’re up against the clock.

Before any big shifts there are always small signals that hint at what’s coming. We’re seeing more and more companies start to make a play for data. Whether it’s as a broker, niche analysis, or in data aggregation. There is risk here if this rapidly growing area is left unchecked.

We build services and solutions using parts provided by other companies. That’s the only way to move forward effectively. When a security or privacy breach happens, how do you handle those parts out of your direct control? Especially considering your customer may not have any idea they exist?

You know you have to master your tools but are you selecting or building the right tools? A lot of teams over or under engineer their tools. This results in either a failure to return the value invested or lost productivity. Are you hitting the sweet spot?
You can’t really remove something from the internet. Not is the owner/operator really wants it out there. That’s a huge advantage and challenge for the internet community. What are the impacts of that fact?

Cyberattack attribution is HARD. But time and time again, we’re seeing attributions—who carried out the attack—made publicly with little to no evidence presented. Worse, these attributions are having real world impacts…

Knowing what the tools in your kit are capable of is critical to success. But can you actually use those features? Do you really understand the implications of the more advanced features of those tools? Sometimes simple is better…and in any case, you better master those tools!

Your product/solution/service has a goal and you’ve probably gotten good at articulating that goal…but is that message resonating with the audience you’re in front of right now? Are you adequately customizing the message for each audience?

“Don’t do work you don’t have to.” It’s a solid rule and one that you can leverage more often than you think. There are opportunities to automate our work all around us, but do you have the skills to take advantage?

Working deeply on any one problem for too long narrows your perspective. That’s just human nature. Are you taking steps to refresh that perspective? To empathize with teams around you?

Trust is a tricky thing. Dotto Tech posed a number of great questions about trust in business and online that got me thinking. Do you trust the technology you’re using? How far? With what data? So many questions, here a few more to help you find some answers…

Nothing is built in isolation. Each technology builds on layers and layers of technology before it. But are those layers worth building on? Can they support the weight of new ideas? How do you account for issues in layers you don’ t control? We’re seeing the negative consequences more and more in the IIoT / OT world…

Decisions are hard enough that you don’t want to have to revisit them constantly. But that’s exactly what is required in the realm of cybersecurity. Do you have a system in place to review decisions? Are you recording the right information to update those decisions when the time comes?
Most teams do not and it’s taking it’s …

User experience is often overlooked when it comes to security and privacy. This leads to some confusing, dangerous, and challenging situations that users are forced into. Why?!?

During a large incident response, bringing everyone together to a “war room” can be the difference in a speedy recovery, but there are downsides as well. The biggest? Fatigue & burnout. How do you monitor and handle that?

There is a ton of news and information on social networks. There’s also a mountain of garbage. How do you sort through it all? Can you? Do we have the tools we need to make sense of the content we’re presented with?

Many questions come along with the federal legalization of cannabis in Canada. It’s a massive example of trickle down risk as various controls around usage and methods of delivery are pushed into areas they weren’t designed for. Are you doing the same thing with your IT deployments? Are you evaluating your risk graph?

Virtual events can be a great way to connect with your audience. They are not only less expensive to run but they are much easier to access for most people. So why are they rarely enjoyable despite having great content?

When you’re trying to teach, pass along a message, or just generally reach anyone, the key is to understand how THEY want to consume information. That’s a huge gap in most communications today, especially breach notification. Put yourself in the audience’s shoes!

Facebook removes 800+ accounts this week, some with massive followings, for political content. The twist? They were US-based, not foreign. What does this mean for our use of social networks?

Google recently conducted a complete security & privacy review of various APIs associated with Google+. The result? The service is shutting down and they found a vulnerability. Did they take the proper steps in disclosing the issue?
With the Bloomberg report on hardware hacking looking more in doubt, more and more politics are coming into play. Anytime you evaluate news, it’s important to look at things objectively. Here are a few tips around evaluating cybersecurity news.

Bloomberg has an absolutely earth shattering report citing a hardware supply chain attack that—they say—impacted several big names. Here’s why this type of attack is so difficult to defend against but also near impossible to execute.

Reflecting back on my keynote at SecTor in Toronto where I delivered some tough new to a roomful of security professionals. Here’s what worked and what could’ve been better!
Criminals are winning the battle against security practitioners. Need proof? Look no further than the new headlines in any given week.
Billions of dollars are being spent on the latest and “greatest” tools, and millions of people hours are being exhausted in the defence of our data. Yet with all this effort, it remains trivially easy for most …
Sometimes you have to deliver really bad news. It’s not your fault, but you’re the one on the hook. How do you deliver it? How do you deliver it without getting mired into the downside?

October is National Cybersecurity Awareness Month (#NCSAM). Look for tons of great content online as the community comes together—globally, not just nationally—to try and raise awareness of cybersecurity and privacy issues.

50 million Facebook accounts were hacked. Facebook responded quickly to the issue but could’ve done better communicating throughout. Here’s what you need to know about the hack.

A recent study proved that Facebook uses more information about you than you realize. Behind the scenes, Facebook compiles “shadow profiles” from various sources in order to better target ads…anyone surprised? 😔

In the recent dust up with the founders of WhatsApp, you might have heard the term “end-to-end encryption”. What is it? What does it means for you? Why was it frustrating efforts to data mine and monetize WhatsApp?

Amazon announced a host of new “Alexa enabled” devices last week. What are the implications for your privacy at home?

Conferences are usually jam packed with great content. So much so that it can be hard to prepare for them and get the most out of them. What do you look for in a conference? How can I help?

Security is a quality issue. Except we don’t treat it that way and that’s costing us dearly.

With the initial set of cybersecurity basics segments done, I’m think it’s worth moving to a “basics” basics series. The goal would be to help everyone understand how the internet works, how email is structure, etc. Thoughts?

Built-in security is always best. That’s “security by design” but when that fails (due to mistakes, oversight, humans), built-in security steps up…or, um, in.
In your personal life you’re assessing risk constantly whether you know it or not. In the digital world the same thing happens BUT you probably don’t have the required context to make an informed decision.

Risk assessments are useful when kept in context and continually updated. A penetration test (or pen test) is when your system undergoes a “friendly” attack with the idea of find issues before cybercriminals do. Together they are a strong set of practices to help you defences.
Personally identifiable information (PII) and Personal Health Information (PHI) are critical concepts. They help identify information that needs additional safeguards and care.

Should you track your children’s every move? Your partners? Family locator apps promise safety and convenience but are they really just an invasion of privacy?

Who did it? It’s a powerful question and the answer to “What is attack attribution?”

Authentication and authorization are two critical concepts that are intertwined. Understanding the difference and their purpose is key to understanding cybersecurity.

Hackers and cybercriminals are all “malicious actors”. While you may not know who is attacking a system, having a better understanding of common motivations is important.

Malicious software (malware) is an umbrella term that covers a number of different types of software designed to do bad things…but those specific categories don’t mean to much day-to-day when it comes to defence…

Perspective is a tricky thing….maybe the hardest aspect of cybersecurity

VPNs can help secure your internet traffic when you’re travelling. They can help you route around geographic restrictions. But is using a VPN exposing you to more risk? What is the impact of centralizing all of your internet requests with one specific company?
What is a password? Why do we use them? Why are they so frustrating? …some answers
Continuing the “basics” series, here’s an easy way to understand the terms: vulnerability, exploit, threat, and risk

The basics starts with understanding the goal of security. It sounds simple but the goal is to make sure whatever you build works as you intend…and only as you intend!

Back from vacation, I recap the show’s structure and new channels as well as the plan around “the basics”

GMail in the classroom just like on your phone. The promise of G Suite for Education is enticing. A low-cost way for schools to provide collaboration tools to students and teachers. But what are the privacy implications of letting the search giant into our schools?

A friend highlighted a real issue: there isn’t enough material about basic cybersecurity that’s easily relatable.
Connecting with others is critical but it can also pose a risk. It’s important not to “leak” information needlessly. This is a practice know as operational security. It’s critically important…and often ignored.

3d printing holds a mountain of promise. While the technology is taking longer than generally expected to make an impact, the areas where it is having an impact are significant. While copyright and outdated thinking get in the way of this technology?

We’re creating more and more data but despite advancements in data processing, we’re still lacking easy to use tools to understand what’s happening around us. What can we do to fix this?
No one wins all the time. Don’t seek out failure but we shouldn’t be afraid of sharing our failures so that others may learn.

Security is there to ensure that the systems you build work only as intended. Part of that is realizing the potential for abuse and ensuring that the system and users can continue to work safely…there’s a LOT of work to do.

A lot of the issues facing our communities and sub communities today (deep fakes, encryption, privacy, DevOps, etc.) need active discussions. By their very nature, you can’t really have discussions at scale…right?

Is that video real? Are you sure? A new technique makes it easier than ever to create passable fake videos of prominent people. You cannot trust your eyes anymore.

Getting your first cybersecurity role can be difficult. Is part of the problem how organizations are hiring talent?

Passwords are a horrible way to verifying identities but they are the best thing we currently have that works at scale. Adding a 2nd factor to that verification significantly increases the security of the system. But how can you add that factor without sacrificing usability?

You cannot stand at “Red Alert” 24/7 but that’s exactly what we do in cybersecurity…often without realizing it. What impact does that have an our approach? Our attitude? Our mental health?

Unchecked assumptions are a major risk in any field…but in cybersecurity they take on a whole new level

A common step when you’re trying to get started in a career in cybersecurity is getting a basic certification. What comes after?

Is your phone trying to trick you into never putting it down? Smartphone addiction has become such a massive problem that the two major operating systems—Apple and Android—now include features designed to help you use your device less. Is this what we have come down to?

It’s all too easy to burnout in IT in general…more so in security. Why? What’s the cost?

Some perceptions override the logic behind risk decisions. How do you fight through to make a sound decision?

Facial recognition is a technology that exemplifies the underlying neutrality of most technology. When used with positive intentions it makes out devices more secure. When in the wrong hands, it can violate privacy on a massive scale. Do we need to regulate this technology? At what level? Regardless of your stance, we need to talk about this as a …

If you’re working by hand, you’re failing. In today’s world of security, rapid delivery, and new technologies, automation is critical.

Getting your first job in cybersecurity can be super frustrating. How can we work through traditional HR processes to get started?

The popular perception of A.I. does not line up with it’s current capabilities. A look at what’s real and what’s not.

Over the few years, mobile has become the dominant platform for gaming. As a result, smaller, simple games have come to prominence. In order to make money developers have (over) rotated on in-app purchases. Fortnite is a great example of an addictive FREE game that is making a ton of money without resorting to trickery.

Design has a massive impact on user behaviour. Sadly, it’s often ignored when it comes to security and privacy.

Google really doesn’t like humans and they LOVE data. At the intersection of those two areas is a new A.I assistant that calls business to complete simple tasks for it’s users and to automatically update Google’s databases: enter Google Duplex.

There’s only upside to collaborating more deeply with other teams in the org. So why doesn’t the security get out there and do it?!?

We’ve spoken a lot of maintaining and expanding perspective when it comes to cybersecurity. In this episode, we dive in highlight a methodology called “service design thinking”.

Tanacon 1.0 was an unmitigated disaster. Not only is this a reminder that physical security is critical but it’s an example of a failure to analyze risk properly (or at all).

We (the IT community) don’t push for cultural change because it requires persistent and dedicated long term work. That runs counter to the usual pace of technology. We (the security community) are even worse off…

Ethical questions and quandaries are tough enough to work though when they are theoretical. But when you’re confronted with them in the real world, there are usually real world consequences. This makes a hard situation even harder. What do you do? What can you do?

How new technologies are used and built is really up to us. Regardless of your moral compass, it’s important that you discuss the creation & use of these tools with your teams and larger community.

Getting started in cybersecurity can be hard. Sticking to core principles is critical as technology will change. But one of the hardest aspects to cultivate is perspective. How can you tackle that challenge?

With iOS 12, Apple will reduce the time an iOS device responds to the USB port when locked down to an hour. Having a hard time understanding why that matters to you? It’s because it really won’t. It is however a gap in the security posture of these devices that Apple is fixing.

G Suite for Education is making waves in the Canadian education market. And why not? It looks like a win-win-win. Too good to be true?

Cryptocurrency is a digital asset. As such, it’s a major target for cybercriminals. We’ve seen attack after attack in the past few months as exchanges, apps, and other players in the cryptocurrency market aren’t aligning their security to the threats they face.

Net Neutrality is a simple dictate that states all network packets must be treated equally. This–of course–tanks a few business models for ISPs and in the US, they have successfully lobbying to remove previously regulations.

As usual there was a host of announcements at WWDC this year. No major spotlight stealers, what does that mean for security?

The push to move to a “DevOps” culture is a great opportunity to improve security. But first, we need to understand the general development workflow!

The DevOps movement is the single biggest opportunity security teams have had in a long time. The goal of DevOps is speed and innovation. That goal can be achieved with systems and automation: why not fully integrate security at the same time for a win-win?

Security and privacy center on trust. You can’t have that without a high level of transparency. In this day and age, everything comes to light eventually. Better to be up front and open with most activities.

Is it just attitude that keeps security teams from working well with the rest of the organization? And if so, can that attitude be changed? What’s keeping things so negative. Some thoughts…

We know that cybersecurity isn’t the best name to describe what is ostensibly, “information security” but it’s the name we’re stuck with.
At some point in the past few years, the term “information security” took a back seat to “cybersecurity”. Does it matter? Why?

I am often asked what a good undergraduate program is to take if someone is aiming for a career in cybersecurity. There are plenty of fantastic options but ironically, one I’m not a fan of is an undergraduate focused purely on cybersecurity!

Most of the focus around cybersecurity education is on the technical aspects. Is that the right approach?

GDPR comes into effect tomorrow and one of it’s biggest advantages is how it will force companies to actually manage their data…well at least personally identifiable information.

Apparently the FBI misrepresented the number of devices they can’t access due to encryption by up to a factor of 6x. This is most likely due to clerical error and a lack of actual statistics rather than malicious intent.

GDPR comes into effect on Friday, 25-May. What does it mean globally? Um…we’re not really sure.

Listening to customers is built into the DNA of a lot of organizations…why aren’t security teams doing the same?

How do you handle data collection from your users? Is it hidden and suspect like the current rash of mobile provider exposures? With no opt-out like Microsoft Office? Or clear and transparent?
Deep thoughts in this episode around ethics in technology and their use. Sparked by the latest issues around mobile phone tracking, this episode tackles the lack of ethics discussions around security and technology.

How can you create a break for yourself to get started on a cybersecurity career path? A few thoughts…

Getting started in cybersecurity isn’t as hard as you think. There’s no “ONE” path but there are a few key attributes that’ll make it easier.

Google announced several new AI advancements at the I/O 2018 event. On the surface, there’s a lot of really usable features. The downside is more profiling and implicit trade offs. I much prefer explicit trades and I think most people agree.
There have been a lot of advancements in AI research and use lately, but are we moving in the right direction? Are we having the right conversations around AIs impact?
AWS re:Invent is the best conference in cloud. This post lays out what you need to know to get the most out of the 2018 edition of this amazing event.

In this episode, I speak to the challenges around today’s cybersecurity and what that means for those just starting down the cybersecurity path.

Facebook wrapped up it’s F8 conference this week with a series of new product announcements. In this episode, we’ll take a look and see how these announcements fit into the bigger picture.

Passwords are the best of a mountain of bad solutions. Picking a strong password lies at the intersection of math (yay!) and psychology…that’s a tough place to be. Here are a few tips on creating a useful, strong password.

Facebook is hosting it’s annual F8 conference and it appears that this will be a reserved year. Understandable given the scandals of late…

When you’re at a conference, one of the biggest perks is the “hallway track”. The serendipitous run-ins with people you follow online, speakers, or other attendees. If you’re not putting yourself out there and meeting some new people, you’re doing yourself a disservice. Get out there and say hi!

The solution for the cybersecurity skills gap? Educate those around you!

Gmail just launched a nice, new redesigned UI. It’s slick and has some great new features. One feature, “Confidential Mode”, is particularly interesting and poorly named/positioned.
This deep techincal dive in the cybersecurity of operational technologies (OT) focuses on the dramatic timing disconnect. Physical technology is often bought to last for years and years, digitally focused tech is designed to be updated constantly and replaced quickly. That’s problem in today’s hostile internet.

Where does the Canadian criminal code stand on hacking? Given how fast technology moves, can the law keep up?

Can new technology solve everything? We in the security community need to spend more time investing in people and process.
Is IP blocking still effective? Is it a sledge hammer when you really need a scalpel?

Cybersecurity is often positioned from the negative. There are bad things coming to get you! What a waste of energy…

Encryption on mobile devices is a challenge for law enforcement. 3rd party companies often use hacks in their products to address this need. Is it right? Is it sustainable?

The FBI and other federal law enforcement in the US (and elsewhere) continue to push back against “going dark”. Thankfully Apple is fighting back, because when we break security systems and processes, no one wins. This post tracks the signficant events in Apple vs. the FBI.
Facebook was called to the carpet and showed well…because they weren’t asked the right questions
It’s often stated that you have to trade usability for security. I call 💩

Streaming is increasing in popularity but how easy is it to go beyond the basics?

All the news and notes from the 2018 AWS Summit in San Francisco
Had enough of the Facebook / Cambridge Analytica scandal yet? Yeah, me too. Thankfully, it’s rolling up to address the bigger issue of digital tracking in general.

After the long weekend, this episode is a bit of a round up. Nothing big jumping out but a few minor issues to address.
We’re tracked everywhere online. Should we be? Is there an upside to this practice?

There’s a lack of easy-to-use tools for “average” users to analyze their data. In today’s world, that means something.

You upload a ton of data to Facebook and in turn, Facebook generates a ton of data about you. I built a tool to take a look at Facebook’s view of you.

Accurate data for cybersecurity threats is hard to come by. That doesn’t mean you can just make it up…

As the Facebook / Cambridge Analytica scandal continues to snowball, we take a look at the larger issues. How does privacy scale? Can it scale under the current social networks? What’s next?

Terms of Service agreements hide all manner of tricks and cede all of the power to the issuing corporation. Should they?

Sometimes the digital world has an impact on the real world…and it’s not always a positive one.

Ugh. Facebook Has Allowed A 3rd Party To Harvest Millions of Credentials
Lots of hype around CPU flaws, ICOs failing, and blockchain. This episode looks to cut through some of it!

CPU Vulnerabilities Seem Like A Massive Problem. Are they deserving of the hype?

My impressions of my first SXSW and the challenges of getting back on stage after a bit of a break

Cybersecurity and privacy are a core part of the fabric of all technology. So why are they missing at most non-security conferences?

“Smart” object are all the rage in our home lives. In the industrial world, operational technologies (OT) has becoming increasingly more connected. That evolution has focused on physical safey, not cyber safety and that’s leading to some significant challenges now that everything is online.

DDoS attacks are scaling to new heights using record numbers of compromised machines. What are your responsibilities to the rest of internet community?

One of the biggest challenges in cybersecurity today is the tendency to secure components instead of the larger system. It’s understandable but also leaves a lot of gaps. How can we change this approach?

In this episode we do a quick recap of the Canadian federal budget announcements around cybersecurity, talk about SXW, and the upcoming launch of the new markn.ca

Rumours swirl ahead of a new Canadian federal budget. Will they address cybersecurity?
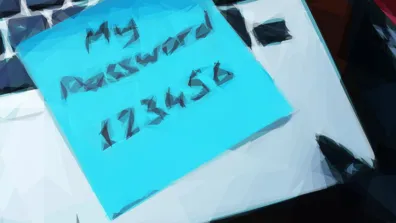
Security awareness is next to useless. Educate users instead

AWS Lambda is a fantastic way to connect various distinct pieces in the cloud. Python is an easily accessible language that makes that work simple. But pulling in 3rd party code can be tricky. This post explains how to package 3rd party modules so you can use them in AWS Lambda.

Passwords are a horrible solution to the challenge of authentication. But they’re the “best” we have for now…right?

DevOps is the “new hotness” but what does it really mean to development, operations, and security?

Voice is going to play a huge role in the future. What are the security and privacy challenges?

Does blockchain finally bring the transparency and accountability needed for an internet scale identity provider?

Good data drives good decisions. This is a major problem in cybersecurity where the data simply isn’t available or accurate.

Cyberattacks happen all of the time. The critical angle to evaluate is their impact. Did the attack breach critical systems? Access personal information?

There is always new threat to worry about in cybersecurity. Keeping perspective about the likelihood of that threat being an actual issue is critical.

Keeping a personal website up to date is always tricky. The technical pieces are simple, it’s be satisfied with the design and making the commitment to focus on the site when there is a ton of other, maybe more interesting work to be done. Needless to say, this is my restarting this site!

AWS re:Invent is the best conference in cloud. This post lays out what you need to know to get the most out of your first time at this amazing show.

Four principles to help you navigate a cloud migration and the realities of hybrid cloud.

Ransomware is the scourge of the digital world. Cybercriminals are making money hand over fist. What can you do to protect yourself?

AWS re:Invent is the best conference in cloud. This post gives you the top five things to focus on to get the most out of the 2016 edition.

AWS re:Invent is the best conference in cloud. This post gives you the top five things to focus on to get the most out of the 2015 edition.

When you hide a message inside of another message, it’s called steganography. While you might not have known it’s name, this technique has a long and colourful history and it is still used today by cybercriminals.
The shared responsibility model defines how the cloud works. This post examines how Shellshock impacts that model.

Recent vulnerability “POODLE” demonstrates how the shared responsibility model helps reduce your security workload.

The shared responsibility model is simple to explain but challenging to implement. This post examines how the models works for the latest Xen hypervisor bug.

AWS continues to expand it’s global network with the opening of a new region in Frankfurt, Germany.

Why do all incident response communications from customers feel the same? Why do they all miss the mark? How hard is it to do better?

Shellshock is a surprising bug. Hidden for decades, what do you need to know to help your organization respond?

Microsoft hosted it’s annual Worldwide Partner Conference and the focus on was Microsoft Azure. I delivered a talk focused on how to automate security operations in Azure.
Code Spaces is the worst case scenario. A simple misconfiguration in the cloud cost them their business.

Cloud computing is more than just fast self-service of virtual infrastructure. Developers and admins are looking for ways to provision and manage at scale.

If you strip away a lot of security terminology, it’s really about understanding what’s going on. If you want slap a fancy term back on, let’s call that “situational awareness”

Microsoft Build 2014 kicks off a new era for Microsoft. One that will (hopefully) transform the company and focus on building out their cloud; Azure.

As AWS opened their summit series for 2014, 5000+ people packed into the Moscone Center. There was a ton of energy in the air and I got to talk about updating security operations for the cloud.

What does a modern security practice look like in the cloud? How do each of the area change?

Forensics is an area that’s often lacking in corporate environments. Few people have time to truly dig into an incident after it’s been resolved. Can we make forensics easier in the cloud?

Network security monitoring is changing dramatically in the cloud as more and more responsibilities are shifted to the Cloud Service Provider. How should your team adjust?

Incident response is often overlooked by everyone outside of the security team. In the cloud, automation and cooperation reign supreme.
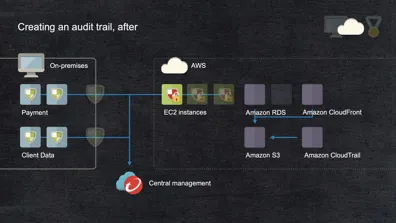
The cloud is a fantastic opportunity to improve your security posture…but only if you update how you handle operations.

The cloud security discussion has changed from ‘should we’ to ‘how do we’. Here are the top issues you should be tackling.

When speaking to security issues in the media, what’s the right level of technical depth?

This post provides information that is designed to help you defend against phishing, spear phishing, and whaling attacks. Exploring the reasons for phishing, spear phishing, and whaling success